Step-by-Step Guides출처: DigitalOcean조회수 22
Hardening SSH: Fail2Ban, Nftables & Cloud Firewalls
By Vinayak Baranwal2026년 2월 23일
**Hardening SSH: Fail2Ban, Nftables & Cloud Firewalls**
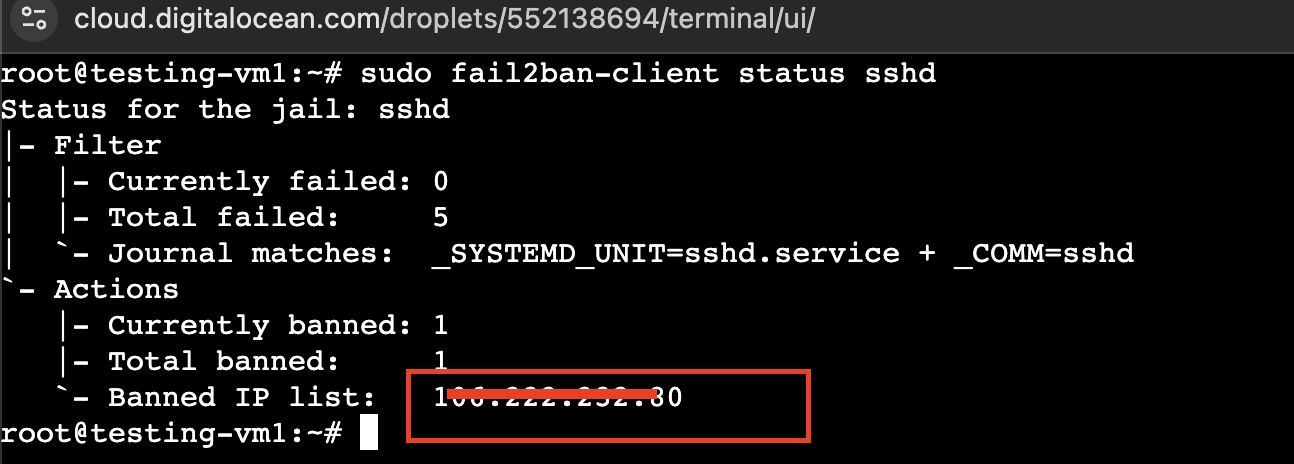
Introduction SSH hardening means reducing the attack surface of your SSH service through configuration, rate limiting, and network controls so that brute-force and unauthorized access are mitigated. Fail2Ban alone is not enough: it reacts after failed logins and modifies the host firewall. It does not replace a firewall, restrict which IPs can reach SSH in the first place, or protect multiple servers through a single entry point. Defense in depth for SSH combines host-level hardening (SSH config, Fail2Ban, nftables) with network-edge controls (DigitalOcean Cloud Firewalls) and a bastion host so that SSH is exposed only where you choose. This tutorial builds on existing DigitalOcean content: for Fail2Ban-only SSH protection see How To Protect SSH with Fail2Ban on Ubuntu; here you get the full stack: hardened SSH, Fail2Ban, nftables, Cloud Firewall, and bastion on DigitalOcean...
---
**[devsupporter 해설]**
이 기사는 DigitalOcean에서 제공하는 최신 개발 동향입니다. 관련 도구나 기술에 대해 더 알아보시려면 원본 링크를 참고하세요.
Introduction SSH hardening means reducing the attack surface of your SSH service through configuration, rate limiting, and network controls so that brute-force and unauthorized access are mitigated. Fail2Ban alone is not enough: it reacts after failed logins and modifies the host firewall. It does not replace a firewall, restrict which IPs can reach SSH in the first place, or protect multiple servers through a single entry point. Defense in depth for SSH combines host-level hardening (SSH config, Fail2Ban, nftables) with network-edge controls (DigitalOcean Cloud Firewalls) and a bastion host so that SSH is exposed only where you choose. This tutorial builds on existing DigitalOcean content: for Fail2Ban-only SSH protection see How To Protect SSH with Fail2Ban on Ubuntu; here you get the full stack: hardened SSH, Fail2Ban, nftables, Cloud Firewall, and bastion on DigitalOcean...
---
**[devsupporter 해설]**
이 기사는 DigitalOcean에서 제공하는 최신 개발 동향입니다. 관련 도구나 기술에 대해 더 알아보시려면 원본 링크를 참고하세요.